FIT – MGT5155 – Week 7
The submissions for this assignment are posts in the assignment’s discussion. Below are the discussion posts for Richard Bocchinfuso, or you can view the full discussion.
“Pen Testing” or Penetration Testing is typically conducted by white hat hackers, also known as ethical hackers. In contrast to black hat hackers who attempt to hack, penetrate, exploit, vandalize, etc. systems the white hat hacker attempts to penetrate a system to identify vulnerabilities so they can be remediated. It is important to realize that vulnerability scans and penetration tests are not synonymous. Vulnerability scans are often automated and inspect systems for known vulnerabilities, while penetration tests focus on attempting to exploit a system, this can be any combination of attack tactics including both social engineering (hacking the human factor) and technical hacking (hacking the machine). (Barnett, 2017) A penetration tester acts as an attacker, adopting the mindset of the attacker. Penetration testers need to possess the technical skills to conduct attacks, but they also need the mind of an attacker. This is why we see famous black hat hackers like Kevin Mitnick running successful cybersecurity businesses like MitnickSecurity (Links to an external site.)Links to an external site.. The move from black hat hacker to white hat hacker is no different than the story told in “Catch Me If You Can” (Links to an external site.)Links to an external site. where Frank Abagnale Jr. makes the move from a check counterfeiter to FBI counterfeiting expert. Thinking like the individual you trying to protect against is key to being a good penetration tester. (CyberVista, 2017)
While penetration testing tools and toolkits are varied there is a process that most testers follow. This process is (Incapsula, n.d.):
- Planning and reconnaissance: Define the scope of the test and gather intelligence. During the planning phase, the tester would determine the testing method. Because penetration testing is an ethical hack the tester is given permission to try to gain access and exploit a system. Testing methods include:
- External Testing: Testing internet accessible assets from outside the internal network.
- Internal Testing: Testing internal assets which are not internet accessible, but that could be attacked but a malicious insider.
- Blind Testing: Test us, here is our company name.
- Double Blind Testing: Same as blind testing, but insiders and security personnel are not informed of the test.
- Targeted Testing: Insiders and security teams work collaboratively. This type of testing is valuable for training security personnel because the pen tester provides real-time information to the security team.
- Scanning: Static and dynamic target inspection. There are various tools to automate scans.
- Gaining access: Access system and exploit vulnerabilities.
- Maintaining access: Determine if access can be persistently maintained.
- Analysis: Compile the results of the penetration test.
Hacking has always been an important learning tool for me. Learning to exploit vulnerabilities can be a fun way to dig deeper into a particular technology and strengthen skills, it’s not always about exploiting something, the process of reverse engineering has often exposed details about a specific technology that I otherwise would not have investigated. I started hacking, cracking and phreaking the mid 1980s, back then I followed Captin Crunch (John Draper) (Links to an external site.)Links to an external site. and phone phreaked, today I am still a 2600 (Links to an external site.)Links to an external site. subscriber and I have added podcasts like Hak5 (Links to an external site.)Links to an external site. to my portfolio of edutainment. In the 80s I was really into BBSes (Bulletin Board Systems) (Links to an external site.)Links to an external site., online communities that pre-date the internet. FidoNet (Links to an external site.)Links to an external site. for life, but I digress, anyone who was BBSing in the 1980s knows that long-distance and exchange costs were painful; let’s just say the blue box (Links to an external site.)Links to an external site. was hard to resist. While I do love playing with application and OS exploits as well as WiFi hacking my current passion is RF hacking.
If you are looking for something to do with that old DirectTV mount I suggest repurposing it for for a high-gain WiFi antenna rig to supercharge your WiFi hacking. Here is a pic of my setup. 🙂

My RF hacking tool of choice is the HackRF One (Links to an external site.)Links to an external site. which I use for fun and to spread awareness of just how insecure the radio waves can be. My neighbors really love when I show them how easy it is for me to lock and unlock their car, pop their trunk, opening their garage door, and disable their alarm system; with their permission of course).
Like any good techie (hacker), my home office is filled with lots of RasperryPis (Links to an external site.)Links to an external site., multiple computers with my hacking machine running Parrot Linux (Links to an external site.)Links to an external site. as opposed to the more mainstream Kali (Backtrack) Linux (Links to an external site.)Links to an external site.. I am a fan of bWAPP (Links to an external site.)Links to an external site. aka a buggy web application to practice skills but I also use Pentester Lab (Links to an external site.)Links to an external site. and Hack This Site (Links to an external site.)Links to an external site. for learning. I have machines running in AWS and OVH, and a rack of equipment in my basement. There aren’t enough toys to keep me entertained.
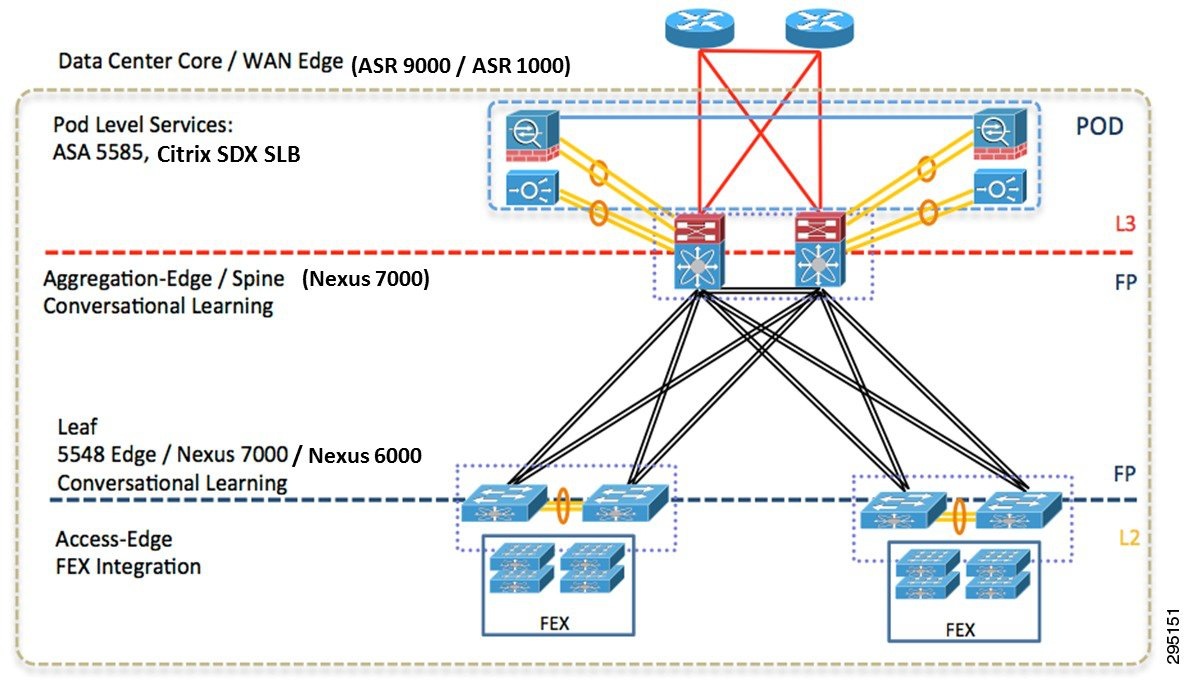
With the explosion of edge technologies and the connected world, the attack surface continues to increase. Today we don’t just need to pen test the glasshouse data center but we have to worry about every edge device, many of which are manufactured with well know exploits. It’s well known that many low-cost Bluetooth can easily be hacked. @jasongorman recently posted the following tweet “Of all the responses by Facebook to some massive data breaches oh and then accidentally possibly helping to end Western democracy, ‘We want to put a webcam in every home’ seems to lack self-awareness” He is referring to the Facebook portal device (Links to an external site.)Links to an external site., and that idea that FB just gave up access to the information of 50 million users, maybe releasing a camera that people can connect to their Facebook account is a bit mistimed. I agree it seems to lack a certain sense of self-awareness or maybe Facebook realizes that the same number of people who read the terms-of-service will care about the hack and not buy the Facebook portal, maybe they are very self-aware and @jasongorman and I are just situationally unaware.
References
Barnett, P. (2017, December 20). Vulnerability Scanning vs. Penetration Testing. Retrieved October 12, 2018, from https://www.secureworks.com/blog/vulnerability-scanning-vs-penetration-testing
CyberVista. (2017, April 24). Penetration Tester: The Secret Agent. Retrieved October 12, 2018, from https://blog.cybervista.net/penetration-tester-cybersecurity-roles
Incapsula. (n.d.). PENETRATION TESTING. Retrieved October 12, 2018, from https://www.incapsula.com/web-application-security/penetration-testing.html
Pentester’s Guide to IoT Penetration Testing. (2018, July 02). Retrieved October 12, 2018, from https://resources.infosecinstitute.com/pentesters-guide-to-iot-penetration-testing/
Christopher, it’s interesting, we hear a lot about how machine learning, deep learning, and artificial intelligence are being used to improve security offerings, everything from SIEM (security information and event management) to antimalware to next-generation firewalls. Cisco calls the use of artificial intelligence in next-generation security products the network intuitive, where the system continuously learns and develops intuition and the ability to infer intent. (Walker, 2017)
What few people realize is that machine learning, deep learning, and artificial intelligence is also being used by hackers. A project called DeepHack where the developers weaponize a machine learning algorithm. (BishopFox, 2017) The technologies for defenders and attackers are getting far more sophisticated, in the future, much will depend on how the user can leverage these underlying complex but powerful technologies. I believe penetration testers will have to learn how to use machine learning frameworks such as TensorFlow, MXNet, and PyTorch.
References
BishopFox. (2017, July 31). Bishop Fox Introduces Hacking AI “DeepHack” at DEF CON 25. Retrieved October 14, 2018, from https://www.bishopfox.com/news/2017/07/bishop-fox-introduces-hacking-ai-deephack-def-con-25/
Walker, K. (2017, June 26). Introducing The Network. Intuitive. Retrieved October 14, 2018, from https://blogs.cisco.com/news/introducing-the-network-intuitive
Carmeshia, I enjoyed the post. The timing of your post is impeccable in the wake of the October 4th Bloomberg Businessweek article (Robertson & Riley, 2018) which stated that the Chinese government (military) was manufacturing microchips that were being placed on motherboards at Chinese factories that manufactured motherboards for Supermicro. The article went on to state that he motherboards went into servers which shipped to dozens of U.S. companies including Amazon and Apple.
Supermicro, Apple and Amazon (Schmidt, 2018) all issued statements of denial, stating that there is no evidence to support the claims made in the Bloomberg report. (Naughton, 2018)
This the truth is not clear here, what is clear is that a country (China) which is a major component manufacturer and a critical supplier to most tech companies has been linked to more than one nation-state attack with a well know cyberwarfare unit (PLA Unit 61398, 2018). Dr A. Theodore Markettos, a Cambridge University researcher, conducted an initial investigation of a key bit of the Supermicro hardware to see if the Bloomberg claim passed what he called “the sniff test” of initial plausibility. He concluded that the Bloomberg report does pass the sniff test. (Markettos, 2018)
Implanting malware on devices during the manufacturing process is nothing new, we’ve seen reports of malware being inserted during the manufacturing process on low-end Android devices (phones and tablets) for years. (Jones, 2018) I expect we haven’t heard the last on the Supermicro saga, it will be interesting to watch it unfold and see how major corporations like Apple and Amazon react.
References
Jones, R. (2018, May 24). More Than 100 Cheap Android Phones Found to Have Malware Preinstalled. Retrieved October 14, 2018, from https://gizmodo.com/a-new-reason-to-not-buy-these-cheap-android-devices-co-1826289219
Markettos, T. (2018, October 5). Making sense of the Supermicro motherboard attack. Retrieved October 14, 2018, from https://www.lightbluetouchpaper.org/2018/10/05/making-sense-of-the-supermicro-motherboard-attack/
Naughton, J. (2018, October 13). The tech giants, the US and the Chinese spy chips that never were… or were they? | John Naughton. Retrieved October 14, 2018, from https://www.theguardian.com/commentisfree/2018/oct/13/tech-giants-us-chinese-spy-chips-bloomberg-supermicro-amazon-apple
PLA Unit 61398. (2018, August 12). Retrieved October 14, 2018, from https://en.wikipedia.org/wiki/PLA_Unit_61398
Robertson, J., & Riley, M. (2018, October 4). The Big Hack: How China Used a Tiny Chip to Infiltrate U.S. Companies. Retrieved October 14, 2018, from https://www.bloomberg.com/news/features/2018-10-04/the-big-hack-how-china-used-a-tiny-chip-to-infiltrate-america-s-top-companies
Schmidt, S. (2018, October 04). Setting the Record Straight on Bloomberg BusinessWeek’s Erroneous Article | Amazon Web Services. Retrieved October 14, 2018, from https://aws.amazon.com/cn/blogs/security/setting-the-record-straight-on-bloomberg-businessweeks-erroneous-article/